|
The iPhone Wiki is no longer updated. Visit this article on The Apple Wiki for current information. |
Difference between revisions of "Unlock"
(→Old AnySim Patch (1.0.X)) |
m |
||
| (46 intermediate revisions by 18 users not shown) | |||
| Line 1: | Line 1: | ||
| + | '''Unlocking''' an [[List of iPhones|iPhone]] means taking an iPhone that is locked to a specific carrier and making it usable on other carriers. |
||
| − | This is the process by which the iPhone baseband is modified to accept the [[SIM]] card of any GSM carrier. This is entirely different than a [[Jailbreak]]. |
||
| + | A software unlock is the process by which the iPhone is modified such that the baseband will accept the [[wikipedia:Subscriber Identity Module|SIM]] card of any GSM carrier. This is entirely different than a [[jailbreak]]; jailbreaking one's iPhone does not unlock it. A jailbreak is, however, required for all currently public, unofficial software unlocks. |
||
| − | ==Official Unlock== |
||
| + | |||
| + | The legality of software unlocking varies in each country; for example, in the US, there is a DMCA exemption for unofficial software unlocking, but the exemption is limited to devices purchased before {{date|2013|01|26}} (so software unlocks for newer devices are in a legal grey area). See [http://www.copyright.gov/fedreg/2012/2012-26308_PI.pdf pages 16-20 of the copyright office's 2012 DMCA rulings] for details. |
||
| + | |||
| + | ==Official unlocks== |
||
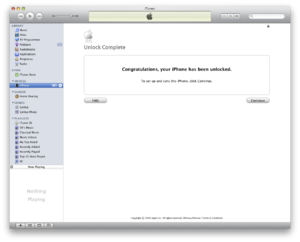
| + | [[Image:iTunesUnlock.png|thumb|Unlock in iTunes]] |
||
At +0x400 in the [[seczone]], a token is stored encrypted with (NCK + NORID + HWID). Apple, knowing the [[NCK]], sends it using an [[activation token]] over iTunes. The phone receives an AT+CLCK="PN",0,"......NCK......" It decrypts the token with the generated [[Baseband_TEA_Keys|key]]. If that decryption, after deRSAing with Key 2, is a valid token for the phone, it is stored back to that flash with the token TEA, but not RSA decrypted. On startup, if the lockstate table says the phone is unlocked, it validates that RSA token. |
At +0x400 in the [[seczone]], a token is stored encrypted with (NCK + NORID + HWID). Apple, knowing the [[NCK]], sends it using an [[activation token]] over iTunes. The phone receives an AT+CLCK="PN",0,"......NCK......" It decrypts the token with the generated [[Baseband_TEA_Keys|key]]. If that decryption, after deRSAing with Key 2, is a valid token for the phone, it is stored back to that flash with the token TEA, but not RSA decrypted. On startup, if the lockstate table says the phone is unlocked, it validates that RSA token. |
||
| + | This type of unlock does not require a jailbreak and is permanent, even surviving a restore (unless Apple or your carrier decides to re-lock the phone, something that has rarely happened [https://discussions.apple.com/thread/2779471]). |
||
| − | ==Old AnySim Patch (1.0.X)== |
||
| + | |||
| − | This deprecated patch disabled signature checks. So the RSA signature would always validate, and the phone would always appear to be unlocked and every NCK would appear to be valid. This patch caused the locktables to be rewritten to the unlocked state which resulted in a cypto failure once the patch was removed during a BB upgrade, causing the 0049 IMEI issue. The virginizer was written in response to this problem and allowed users to write locked, virin locktables. This removed the crypto failure and allowed the application of the ignore MCC/MCN patch. |
||
| + | ==Software unlocks== |
||
| + | This is a way to unlock your iPhone for free with a package from Cydia, however, it only works on selected basebands. The unlock-able basebands and tools are listed below. |
||
| + | ===[[yellowsn0w]]=== |
||
| + | * 02.28.00 |
||
| + | |||
| + | ===[[Ultrasn0w]]=== |
||
| + | |||
| + | ====iPhone 3G/3GS==== |
||
| + | * 04.26.08 |
||
| + | * 05.11.07 |
||
| + | * 05.12.01 |
||
| + | * 05.13.04 |
||
| + | * 06.15.00 |
||
| + | ====iPhone 4==== |
||
| + | * 01.59.00 |
||
| + | |||
| + | ===[[BootNeuter]]=== |
||
| + | * 04.05.04_G |
||
| + | |||
| + | ===[[blacksn0w]]=== |
||
| + | * 05.11.07 |
||
| + | |||
| + | ==[[Hardware unlock]]== |
||
| + | The first iPhone unlocking method (for the [[M68AP|original iPhone]]) actually required opening up your phone. |
||
| + | |||
| + | Currently, it isn't possible to hardware unlock current devices; the closest thing would be [[SIM hacks]], which function as interposers, not a hardware modification. |
||
| + | |||
| + | ==Old AnySim Patch (1.0.x)== |
||
| + | This deprecated patch disabled signature checks. So the RSA signature would always validate, and the phone would always appear to be unlocked and every NCK would appear to be valid. This patch caused the locktables to be rewritten to the unlocked state which resulted in a cypto failure once the patch was removed during a baseband upgrade, causing the 0049 IMEI issue. The [[virginizer]] was written in response to this problem and allowed users to write locked, virgin locktables. This removed the crypto failure and allowed the application of the ignore MCC/MNC patch. |
||
==New AnySIM Patch (1.1+)== |
==New AnySIM Patch (1.1+)== |
||
This patch, also know as the ignore MCC/MNC patch, makes every MCC/MNC pair appear valid. This patch is overwritten on a reflash of the baseband, and doesn't touch the seczone or the locktables at all. It must be reapplied for every baseband upgrade to maintain the unlock. |
This patch, also know as the ignore MCC/MNC patch, makes every MCC/MNC pair appear valid. This patch is overwritten on a reflash of the baseband, and doesn't touch the seczone or the locktables at all. It must be reapplied for every baseband upgrade to maintain the unlock. |
||
| + | In addition, AnySIM 1.1 fixed the "Spamming AT" problems from [[iUnlock]] and earlier AnySIM versions. |
||
| − | ==IPSF== |
||
| + | |||
| − | See [[IPSF]] for main article. This exploit changed the lockstate table in the [[seczone]] to read unlocked and created a spoofed RSA token that was seen as valid by BL3.9 (BL4.6 was ''not'' vulnerable to IPSF). It overwrote your previous token, which means the phone could nor longer be officially unlocked, unless a restore of the token was performed from a previously made backup. Since the token isn't modified in a baseband flash, this unlock survived a baseband downgrade or upgrade. Apple attempted to combat this by requiring AT+CLCK command to be sent every startup. In a officially unlocked iPhones, lockdownd does this. In a late verion IPSF phone, signal.app does this. |
||
| + | ==[[IPSF]]== |
||
| + | This exploit changed the lockstate table in the [[seczone]] to read unlocked and created a spoofed RSA token that was seen as valid by [[Baseband Bootloader|bootloader]] 3.9 (4.6 was ''not'' vulnerable to IPSF). It overwrote your previous token, which means the phone could no longer be officially unlocked, unless a restore of the token was performed from a previously made backup. Since the token isn't modified in a baseband flash, this unlock survived a baseband downgrade or upgrade. Apple attempted to combat this by requiring AT+CLCK command to be sent every startup. In a officially unlocked iPhones, lockdownd does this. In a late version IPSF phone, signal.app does this. |
||
== Cloning Officially Unlocked Phones == |
== Cloning Officially Unlocked Phones == |
||
This has been suggested by many people, however it has been well investigated and virtually ruled out for these reasons: |
This has been suggested by many people, however it has been well investigated and virtually ruled out for these reasons: |
||
| − | # Replacing the [[Baseband Bootloader|baseband |
+ | # Replacing the [[Baseband Bootloader|baseband bootloader]] or [[Baseband Firmware|firmware]] of a locked phone with that of an officially unlocked phone does ''not'' unlock the phone, as the unlock information resides in a different flash area, known as the [[seczone]] and is unique to each phone. |
| − | # |
+ | # Cloning the [[seczone]] would duplicate [[wikipedia:International Mobile Equipment Identity|IMEIs]] which would be illegal in most places and would likely result in a ban of these. |
| − | # |
+ | # Phones with cloned [[seczone]]s would not even be unlocked by the [[NCK]]s of the phone they were cloned from as the [[CHIPID]] and [[NORID]] is concatenated with the [[NCK]] to produce the decryption key used on the RSA [[seczone]] token. The only way to make this work is to change the [[NORID]] and [[CHIPID]] which is not possible. |
| + | |||
| + | ==Ultrasn0w== |
||
| + | After the S-Gold 2 days, user land exploits are used to unlock the current devices and basebands, which are usually exploited with [[ultrasn0w]], [[yellowsn0w]], [[PurpleSn0w]] or [[Blacksn0w]]. Those Softwares exploited several injunction vectors, such as [[AT+XAPP]], [[AT+XLOG]] or [[AT+XEMN]] |
||
| + | |||
| + | == External Links == |
||
| + | *[http://thejailbreaknews.com/once-again-officially-legal-to-unlock-your-iphone/ Once Again Officially Legal to Unlock Your iPhone] |
||
| + | *[http://caniunlock.com/ English Website from chpwn with overview of unlock status] |
||
| + | *[http://www.slideshare.net/slides_luis/baseband-playground-10652487 "Baseband Playground" a presentation by Luis Miras about all current unlocks] |
||
| + | *[http://conference.hitb.org/hitbsecconf2012ams/materials/D1T2%20-%20MuscleNerd%20-%20Evolution%20of%20iPhone%20Baseband%20and%20Unlocks.pdf Evolution of the iPhone Baseband and unlocks by MuscleNerd] |
||
| + | [[Category:Unlocking Methods]] |
||
| − | The only way to possibly make this work is to change the NORID and CHIPID which is impossible. Ergo, this is impossible. |
||
Latest revision as of 18:42, 16 September 2021
Unlocking an iPhone means taking an iPhone that is locked to a specific carrier and making it usable on other carriers.
A software unlock is the process by which the iPhone is modified such that the baseband will accept the SIM card of any GSM carrier. This is entirely different than a jailbreak; jailbreaking one's iPhone does not unlock it. A jailbreak is, however, required for all currently public, unofficial software unlocks.
The legality of software unlocking varies in each country; for example, in the US, there is a DMCA exemption for unofficial software unlocking, but the exemption is limited to devices purchased before 26 January 2013 (so software unlocks for newer devices are in a legal grey area). See pages 16-20 of the copyright office's 2012 DMCA rulings for details.
Contents
Official unlocks
At +0x400 in the seczone, a token is stored encrypted with (NCK + NORID + HWID). Apple, knowing the NCK, sends it using an activation token over iTunes. The phone receives an AT+CLCK="PN",0,"......NCK......" It decrypts the token with the generated key. If that decryption, after deRSAing with Key 2, is a valid token for the phone, it is stored back to that flash with the token TEA, but not RSA decrypted. On startup, if the lockstate table says the phone is unlocked, it validates that RSA token.
This type of unlock does not require a jailbreak and is permanent, even surviving a restore (unless Apple or your carrier decides to re-lock the phone, something that has rarely happened [1]).
Software unlocks
This is a way to unlock your iPhone for free with a package from Cydia, however, it only works on selected basebands. The unlock-able basebands and tools are listed below.
yellowsn0w
- 02.28.00
Ultrasn0w
iPhone 3G/3GS
- 04.26.08
- 05.11.07
- 05.12.01
- 05.13.04
- 06.15.00
iPhone 4
- 01.59.00
BootNeuter
- 04.05.04_G
blacksn0w
- 05.11.07
Hardware unlock
The first iPhone unlocking method (for the original iPhone) actually required opening up your phone.
Currently, it isn't possible to hardware unlock current devices; the closest thing would be SIM hacks, which function as interposers, not a hardware modification.
Old AnySim Patch (1.0.x)
This deprecated patch disabled signature checks. So the RSA signature would always validate, and the phone would always appear to be unlocked and every NCK would appear to be valid. This patch caused the locktables to be rewritten to the unlocked state which resulted in a cypto failure once the patch was removed during a baseband upgrade, causing the 0049 IMEI issue. The virginizer was written in response to this problem and allowed users to write locked, virgin locktables. This removed the crypto failure and allowed the application of the ignore MCC/MNC patch.
New AnySIM Patch (1.1+)
This patch, also know as the ignore MCC/MNC patch, makes every MCC/MNC pair appear valid. This patch is overwritten on a reflash of the baseband, and doesn't touch the seczone or the locktables at all. It must be reapplied for every baseband upgrade to maintain the unlock.
In addition, AnySIM 1.1 fixed the "Spamming AT" problems from iUnlock and earlier AnySIM versions.
IPSF
This exploit changed the lockstate table in the seczone to read unlocked and created a spoofed RSA token that was seen as valid by bootloader 3.9 (4.6 was not vulnerable to IPSF). It overwrote your previous token, which means the phone could no longer be officially unlocked, unless a restore of the token was performed from a previously made backup. Since the token isn't modified in a baseband flash, this unlock survived a baseband downgrade or upgrade. Apple attempted to combat this by requiring AT+CLCK command to be sent every startup. In a officially unlocked iPhones, lockdownd does this. In a late version IPSF phone, signal.app does this.
Cloning Officially Unlocked Phones
This has been suggested by many people, however it has been well investigated and virtually ruled out for these reasons:
- Replacing the baseband bootloader or firmware of a locked phone with that of an officially unlocked phone does not unlock the phone, as the unlock information resides in a different flash area, known as the seczone and is unique to each phone.
- Cloning the seczone would duplicate IMEIs which would be illegal in most places and would likely result in a ban of these.
- Phones with cloned seczones would not even be unlocked by the NCKs of the phone they were cloned from as the CHIPID and NORID is concatenated with the NCK to produce the decryption key used on the RSA seczone token. The only way to make this work is to change the NORID and CHIPID which is not possible.
Ultrasn0w
After the S-Gold 2 days, user land exploits are used to unlock the current devices and basebands, which are usually exploited with ultrasn0w, yellowsn0w, PurpleSn0w or Blacksn0w. Those Softwares exploited several injunction vectors, such as AT+XAPP, AT+XLOG or AT+XEMN